The future of RFID technology is growing and expanding as more industries and organisations are incorporating this technology.
When it comes to security, the world of RFID access control systems can seem quite complicated and indecipherable. Whether you are exploring physical access control for the first time or upgrading an existing setup, understanding the fundamentals of RFID is essential.
To help you better navigate the RFID-based access control jungle, we’ve created this handy quick guide.
What Is RFID Access Control?
Radio Frequency Identification (RFID) utilises electromagnetic fields to automatically identify and track various objects. Most RFID systems include a microchip with an antenna (tag), a reader with an antenna and an access control server.
An RFID system cross-references the data stored on the tag with its own database. If it matches, the access is then granted.
RFID Frequencies
Frequency is the length of the radio waves used to communicate between system elements. RFID technology incorporates various frequency levels that determine the solution’s reading range. The lower the frequency, the shorter the reader’s range. Below are some of the most common frequency ranges:
- Low Frequency 120 - 150 kHz (LF)
- High Frequency 13.56 MHz and higher (HF)
- Ultra-High Frequency 860 - 980 MHz (UHF)
- Microwave Frequency 2.45 GHz and higher
Understanding the frequencies at which RFID systems operate will help you to choose the right solution for your application. Radio waves operate differently at each of these frequencies and there are pros and cons associated with using each frequency band.
An RFID access control system with a lower frequency can read better near liquid or metal surfaces, however, it has a slower data read rate. Higher frequency systems have faster data transfer rates and longer read ranges but are more sensitive to radio wave interference caused by liquids and metals in the environment.
That being said, rapid technology advancements in recent years have made it possible to use ultra-high frequency RFID systems around liquids and metals.
RFID Tags
RFID tags consist of three key elements: a microchip, antenna and a substrate. The microchip within the tag is what stores and processes information, modulates and demodulates radio-frequency signals. And antenna enables the tag to receive and transmit the signal. For a comparison of RFID tags against another common identification technology, see our guide on RFID tags vs QR codes.
RFID tags can be differentiated by their power supply. There are two main types of tags used in the access control industry - passive and active tags. These tags are embedded in a variety of credentials including cards and fobs — learn about the differences between proximity cards and key fobs to choose the right form factor.
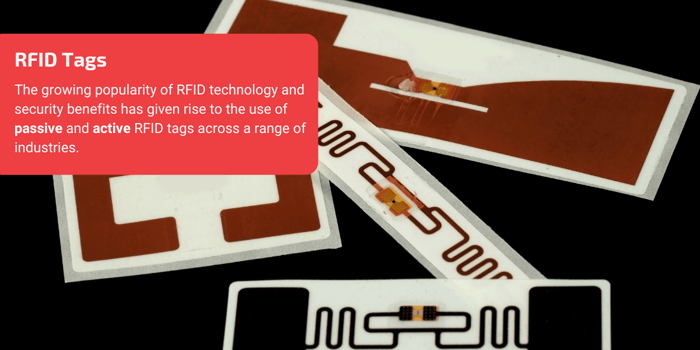
Passive VS. Active Tags
A passive RFID tag doesn’t include a battery; therefore, its built-in antenna picks up on the electromagnetic waves that are sent out by the reader.
These tags tend to be less expensive compared to active tags, and therefore could be a cost-effective solution for companies with a tight budget. They are also smaller in size as they don’t need to carry a battery.
However, they also have their limitations. As passive tags don’t have a power source of their own, they require extra time for charging before conducting any data transmission. They also tend to have fewer data storage capacity compared to active tags.
Active RFID tags have a built-in battery power allowing it to transmit the data stored on to it directly to the reader continuously.
Even though their batteries do have a limited lifetime, it usually does last for years. Tag’s battery-powered response makes it a perfect solution for applications where RF signals might encounter interference.
Added to this benefit is the fact that active tags have an extensive reading range. However, all these additional features come at a price - active tags tend to be more expensive than passive tags.
How Does RFID Access Control Work?
As mentioned above, an RFID access control system usually consists of a tag, a reader with an antenna and an access control server.
The card reader is constantly emitting a radio frequency energy field. Therefore, when the card enters the field, the power from the RF field energises an aerial of copper wire inside the card. The wire is connected to the smart card chip inside the card.
The aerial powers the chip containing ID number and any other data contained on the card, such as unique customer or facility code. This ID number is then sent back to the reader.
Finally, the reader sends the card number to the access control system which will decide on whether the cardholder is authorised to enter.
Once the lock on the door has received this signal from the card reader, it can then be opened using the door’s lockset or push-bar.
In addition, employees won’t have to worry about locking the door behind them as the magnetic lock system will do that automatically. This helps to ensure that the door is secured after every time access is granted.
Benefits of RFID Access Control
Increased security
RFID-based access control systems contribute to improved security of business premises. Businesses don’t need to worry about unauthorised people entering their building. Each card is connected to an individual’s identifying information, so if the card got stolen, it would be easy to pinpoint the intruder using the stolen card.
Easier and Faster Access
A long-range RFID-based electronic ID badge allows an authorised member of staff to access secured areas within the premises without the need to use their hands to present the card to a reader, enabling them to enter the premises with ease. This is especially important for applications where employees have to carry heavy objects and equipment.
Integration
Long-range RFID is a complete people and vehicle solution. This technology is an ideal solution for automatic vehicle identification, granting access to approaching vehicles automatically without the need of a manned gate, ticket stations, or pin pads.
This means that members of staff can now go from their doorstep to their workplace - all with the help of one card. A building access card goes into a special holder in the car, allowing seamless vehicle access into the premises.
Manage the Flow of Staff Members
An efficient access control solution can enable organisations to track and monitor staff members and visitors with the help of access control software. This software offers real-time data relevant to each staff member that is stored and archived to be used later on in reports.
Therefore, managers have all the data on key staff members and their movements within the building.
In the case of unusual event or crisis, a surveillance system that is connected to the readers, can notify access control system to lock or unlock certain doors, or revoke access to particular people in cases that their badge was stolen.
RFID vs Other Card Reader Types
RFID-based proximity readers are among the most popular access control solutions, but they are not the only option. Below is a comparison of RFID against the other major card reader technologies, highlighting where each excels and where RFID holds the advantage.
| Technology | How It Works | Strengths Over RFID | Why RFID Is Often Preferred |
|---|---|---|---|
| Magnetic Stripe | Reads data from a magnetic stripe when swiped through the reader. | Lower upfront cost; universally recognised across legacy systems. | Mag-stripe cards suffer from physical wear and tear, require contact (swipe), and offer limited encryption — making them easier to clone and less secure than RFID. |
| Wiegand | Uses the Wiegand magnetic effect with specialised wiring for data transmission. | Exceptional durability; supports multiple verification factors for enhanced security. | Wiegand systems carry a higher upfront cost and require specialised installation expertise. RFID delivers comparable durability at a lower total cost with simpler deployment. |
| Biometric | Authenticates users via unique biological traits such as fingerprints, facial recognition, or eye scans. | Highest possible security — biometric data cannot be lost, forgotten, or easily shared; supports dual authentication (biometric + card/PIN). | Biometric readers are significantly more expensive, can produce false negatives due to environmental factors (dirt, moisture, oils), and raise data-privacy considerations. RFID offers strong security without these operational sensitivities. |
| Smart Card | Communicates with a microprocessor embedded in the card, enabling advanced encryption and multi-function use. | Superior encryption algorithms; cards can serve double duty for data storage or cashless payments. | Smart card systems require specialised cards and readers with higher initial costs, and may not be backward-compatible with older infrastructure. RFID provides a strong balance of security and cost-efficiency without the compatibility hurdles. |
| NFC | Uses short-range (4 cm) high-frequency communication, often via smartphones or smart cards through NFC readers. | Two-way communication; smartphone credentials; strong encryption at close range. | Limited to very short range, making it unsuitable for hands-free or vehicle applications. RFID offers far greater read distances while NFC is better suited to tap-based entry. |
| Infrared & Bluetooth | Uses wireless signals from smartphones or dedicated devices for hands-free access. | Smartphone integration eliminates the need to carry a physical card; convenient hands-free operation. | Wireless protocols introduce additional attack surfaces (hacking, signal interception) and higher power consumption. RFID achieves hands-free access at long range (up to 10 m with UHF) while maintaining a simpler, lower-power architecture. |
Key takeaway: RFID strikes an effective balance between security, cost, durability, and ease of use. Magnetic stripe and Wiegand readers may suit specific legacy or high-durability scenarios, biometric readers are ideal where maximum security justifies the expense, and smart card or Bluetooth readers shine in multi-function or mobile-first environments. For a closer look at how NFC compares to Bluetooth in access control, see our dedicated guide. For most access control applications, however, RFID remains the versatile, cost-effective choice.
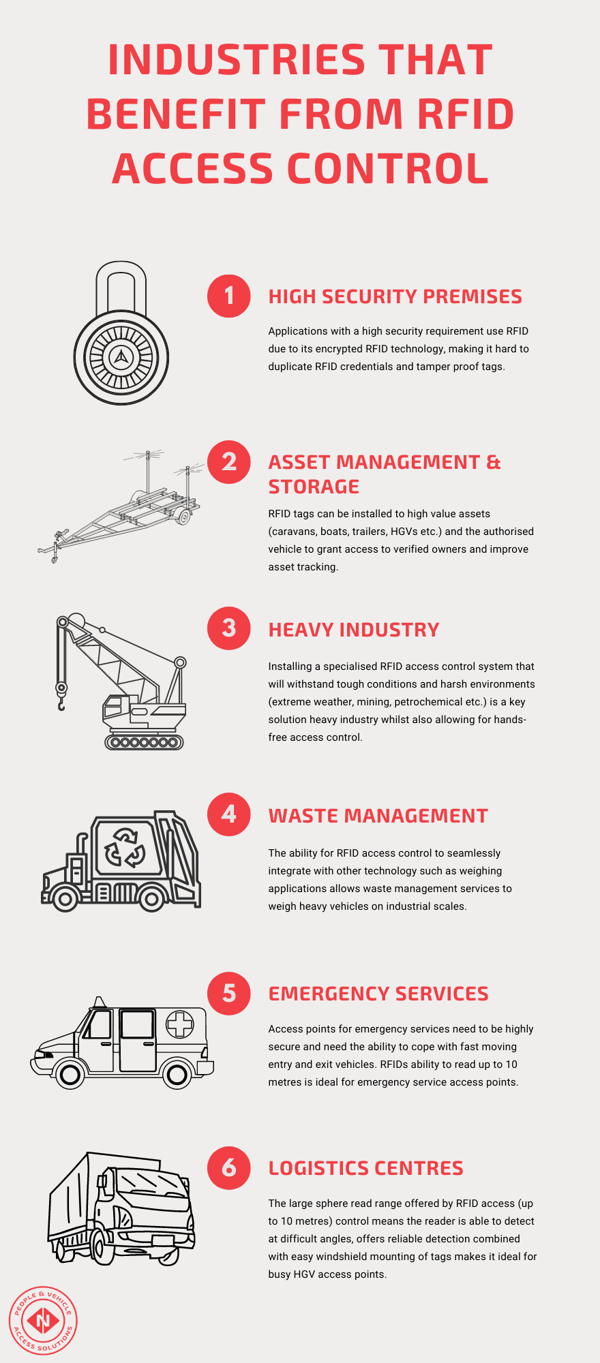
What Industries can Benefit from RFID Access Control?
Due to its superior security capabilities and ability to integrate with a wide range of applications from vehicle access control to time attendance, RFID access control can help a wide range of industrial applications.
An effective access control system can be used with:
- High security premises; the encrypted RFID technology and use of tamper-proof tags makes it suited to premises with a high security requirement. Credentials range from proximity cards and key fobs to NFC-enabled smart cards depending on the level of security needed.
- RFID Asset management and storage applications; RFID tags can be added to a range of assets from high value objects to caravans. The ability to tag objects and their corresponding owners makes RFID a popular solution within asset management.
- Heavy industry and manufacturing; Choosing a durable access control solution that will last is important in harsh environments such as mining, extreme weather, petrochemical and other heavy industries. There are a number of RFID readers and corresponding tags purpose built to survive harsh environments whilst providing hands-free access to personnel carrying heavy equipment.
- Waste management; Waste management services have a number of unique requirements such as the need to weigh heavy vehicles on industrial scales. RFID access control is able to seamlessly integrate with weighing applications, expanding its capabilities beyond just access control.
- Emergency services; High volume access points that also need to be restricted to emergency personnel often require access control that can cope with hands-free entry. RFID’s ability to read up to 10 metres is perfect for busy environments that need to maintain an element of security.